Navigating the complex landscape of modern digital environments means acknowledging the inevitable: computer incidents will occur. Whether it’s a minor system glitch, a malware infection, or a full-scale data breach, the way an organization responds can significantly impact its recovery, reputation, and long-term security posture. A robust and clear Computer Incident Report Template is not merely a bureaucratic formality; it’s a critical tool for structured response, effective analysis, and continuous improvement in cybersecurity.
The immediate aftermath of an incident can be chaotic, making a standardized reporting mechanism invaluable. Without a predefined template, crucial details can be overlooked, communication can become fragmented, and the overall response can be less efficient. This lack of structure can lead to delayed recovery, increased costs, and even regulatory non-compliance.
Beyond the immediate crisis, a well-documented incident history provides a rich source of data for trend analysis, risk assessment, and policy refinement. It allows organizations to identify recurring vulnerabilities, measure the effectiveness of their security controls, and make informed decisions about future investments in cybersecurity infrastructure and training.
This article will delve into the essential elements of a comprehensive computer incident report, exploring why each section is important and how a standardized template can empower your organization to respond more effectively. We will cover best practices for its implementation, customization, and how it integrates into a broader incident management framework, ensuring that every digital disruption becomes an opportunity for growth and enhanced resilience.
The Indispensable Role of Incident Reporting in Cybersecurity
In today’s digital-first world, cybersecurity incidents are not a matter of “if,” but “when.” From phishing attempts and ransomware attacks to insider threats and accidental data leaks, the spectrum of potential incidents is vast. Effective incident reporting serves as the backbone of an organization’s incident response strategy, transforming chaotic events into manageable, analyzable data points. It ensures that every incident, regardless of its perceived severity, is captured, documented, and reviewed systematically.
A primary function of incident reporting is to establish a clear, chronological record of events. This record is vital for several reasons: it aids in forensic analysis, supports legal and compliance requirements, and provides a basis for post-incident reviews. Without accurate and timely reporting, the chain of events can become obscured, hindering efforts to understand the root cause and prevent recurrence. Moreover, it fosters a culture of accountability within an organization, encouraging employees to report suspicious activities without fear, knowing their input contributes to collective security.
Defining a Computer Incident
Before diving into reporting, it’s crucial to understand what constitutes a “computer incident.” Generally, a computer incident refers to any event that compromises the confidentiality, integrity, or availability of an information system or the information it processes, stores, or transmits. This definition is broad by design to encompass a wide array of occurrences.
Examples include:
* Security Breaches: Unauthorized access to systems or data, data exfiltration, or intellectual property theft.
* Malware Infections: Viruses, ransomware, spyware, or Trojans affecting systems or networks.
* System Failures: Unexpected hardware malfunctions, software crashes, or network outages that disrupt operations.
* Policy Violations: Unauthorized use of company resources, improper data handling, or non-compliance with security policies.
* Denial-of-Service (DoS) Attacks: Attempts to make a machine or network resource unavailable to its intended users.
* Phishing and Social Engineering: Successful attempts to trick users into revealing sensitive information or executing malicious code.
Recognizing these diverse types of incidents is the first step toward effective reporting, as the nature of the incident will dictate the specific details and actions required in the report.
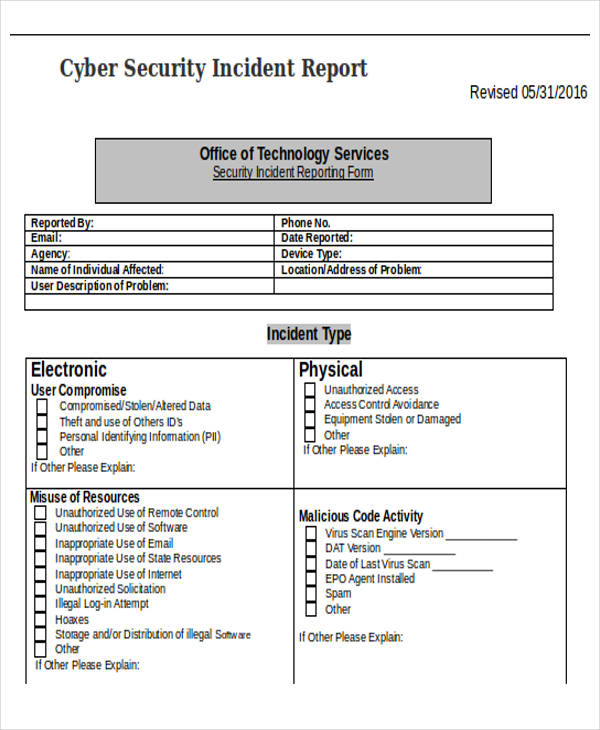
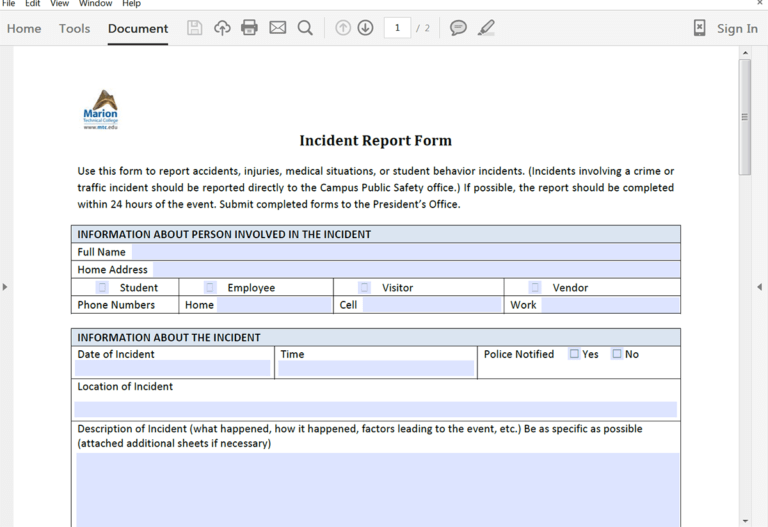
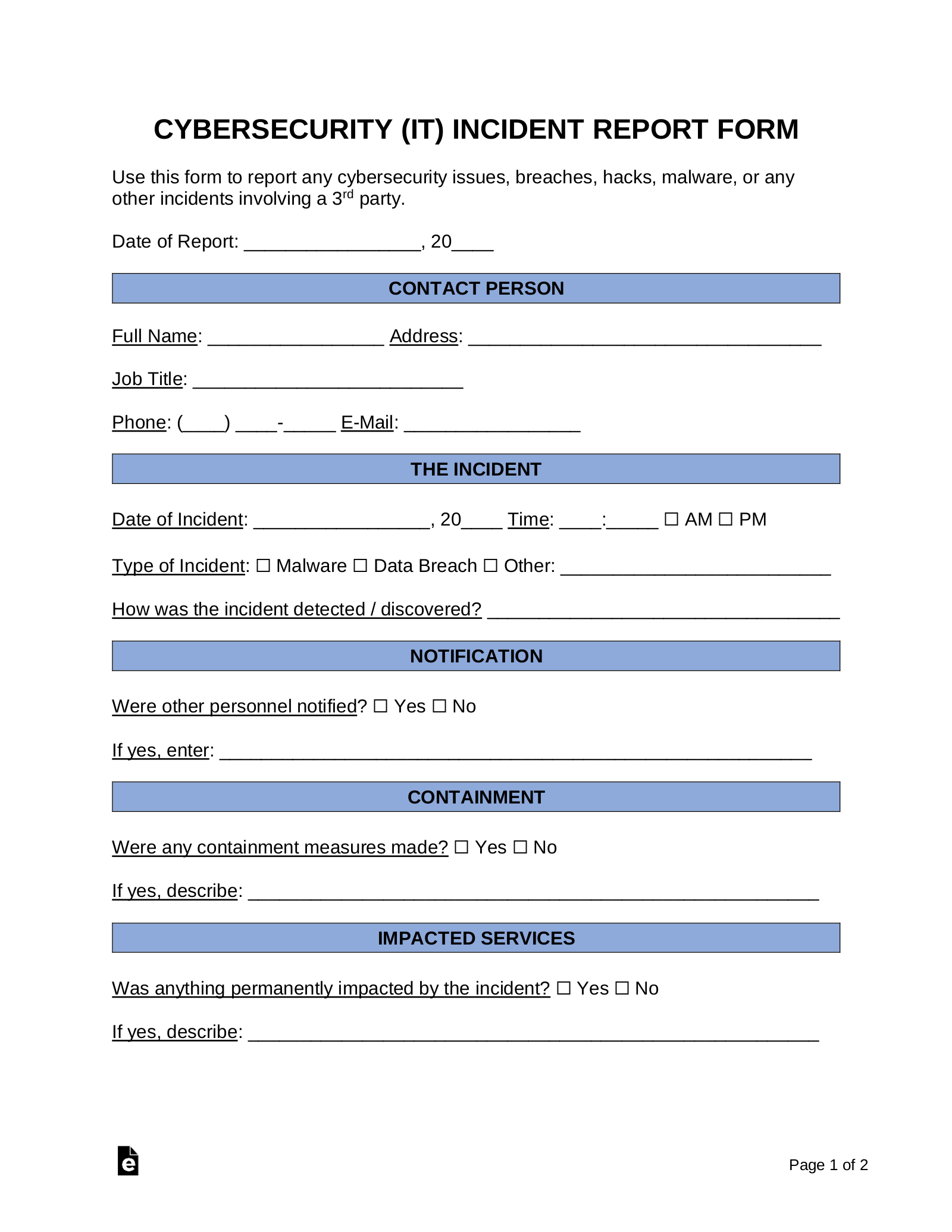
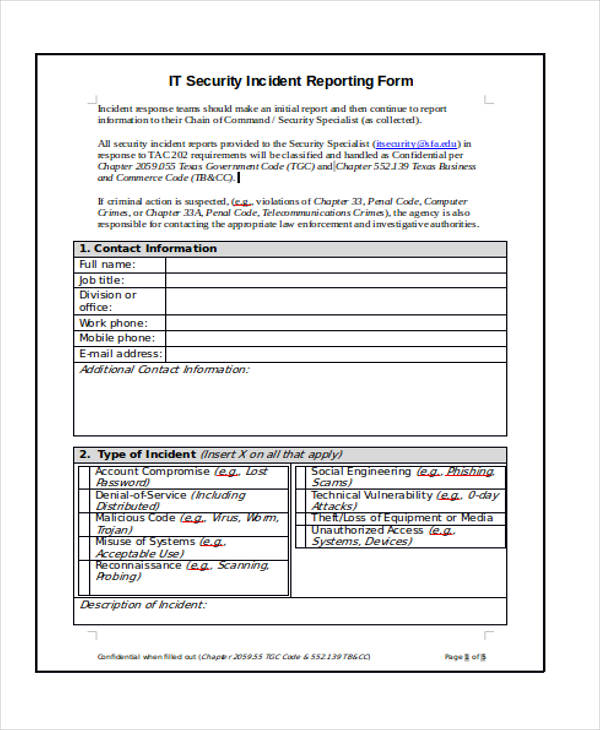
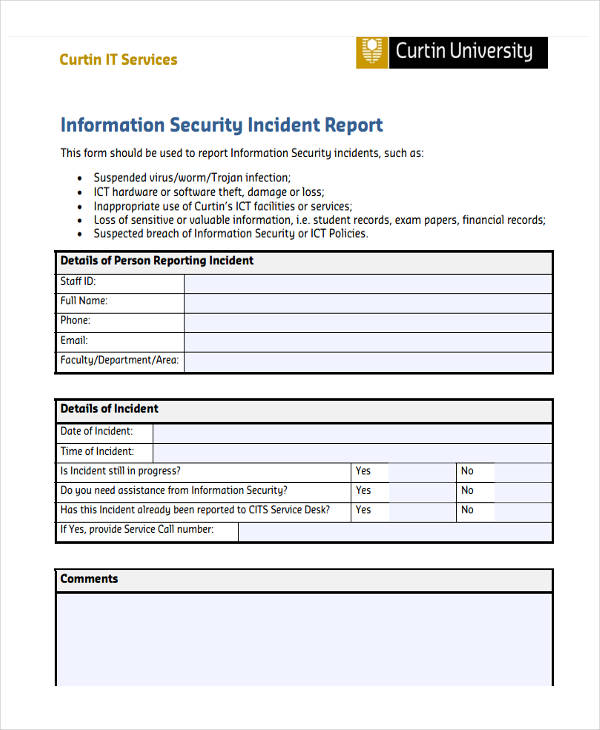
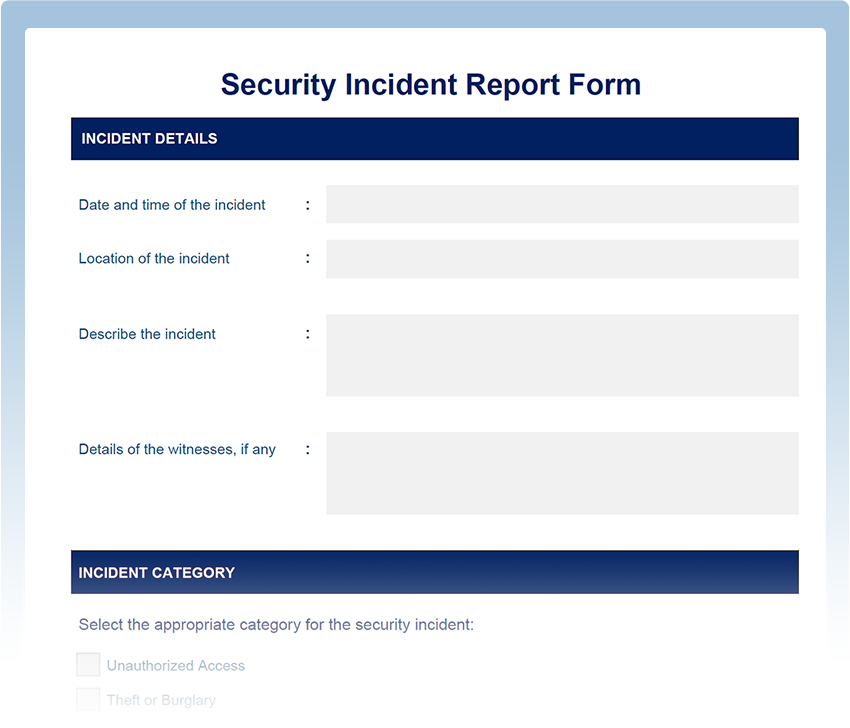
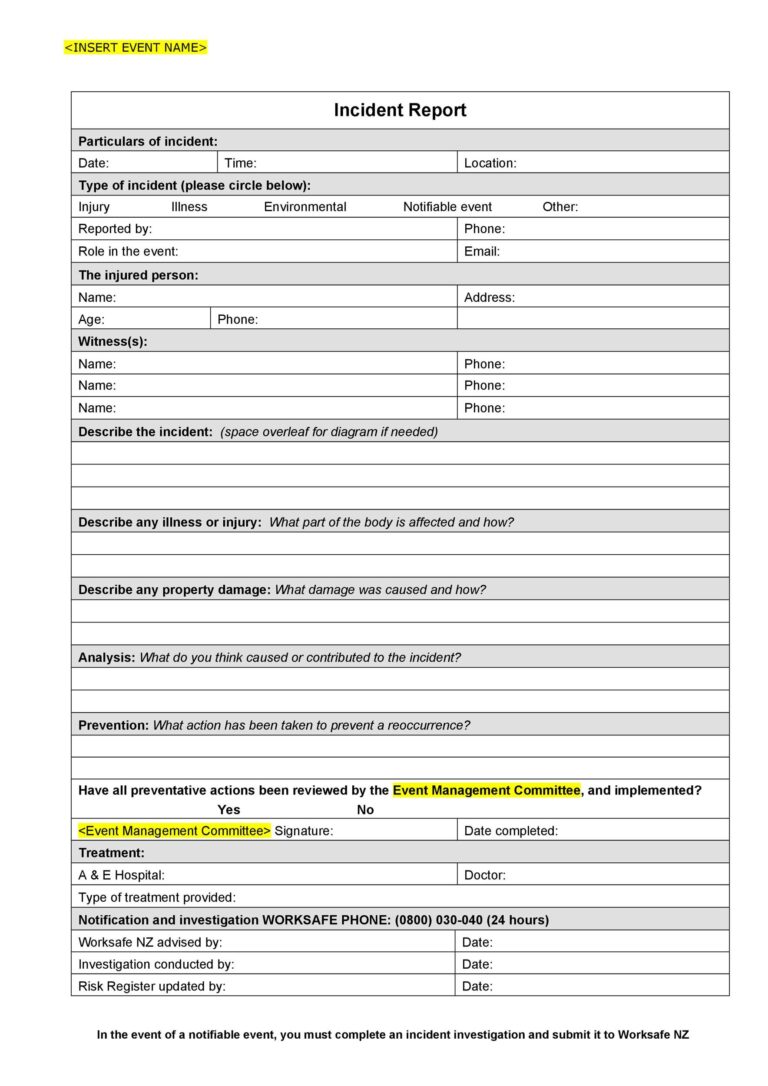
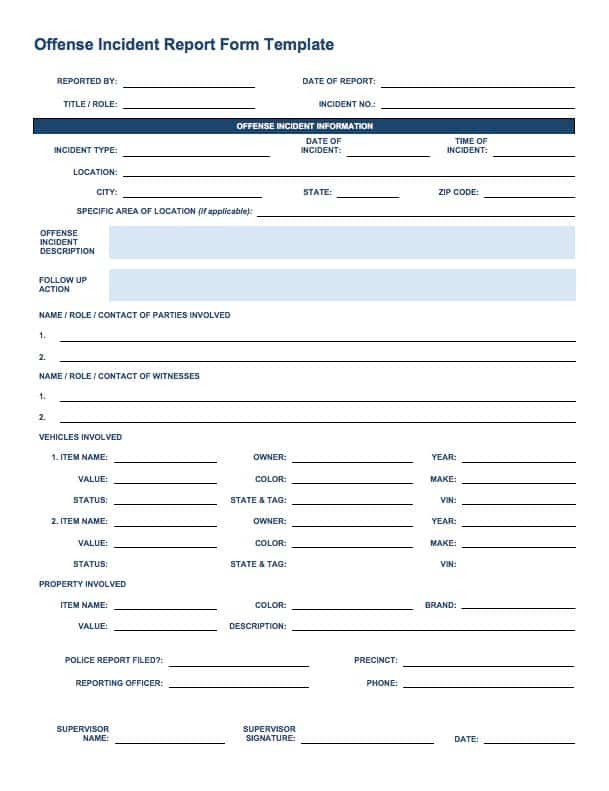
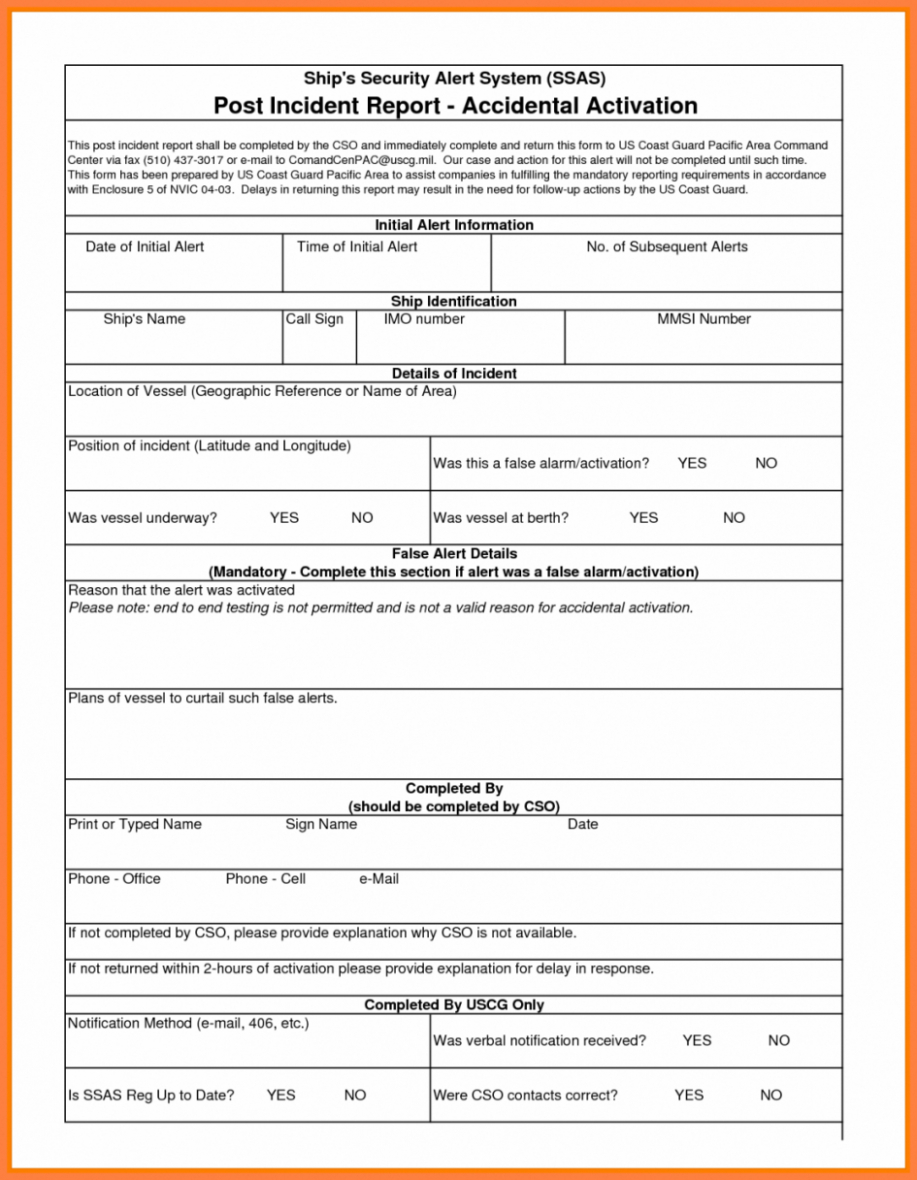
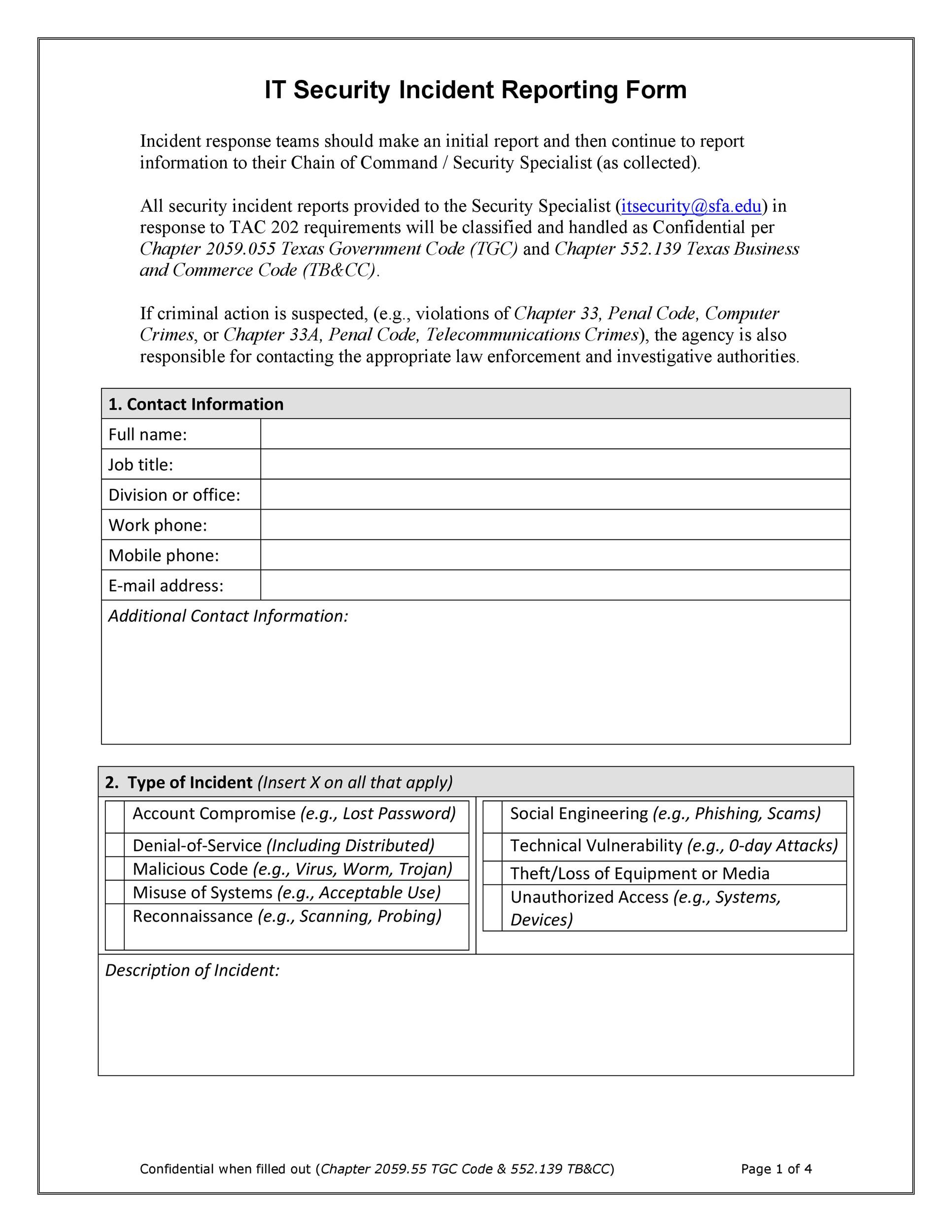
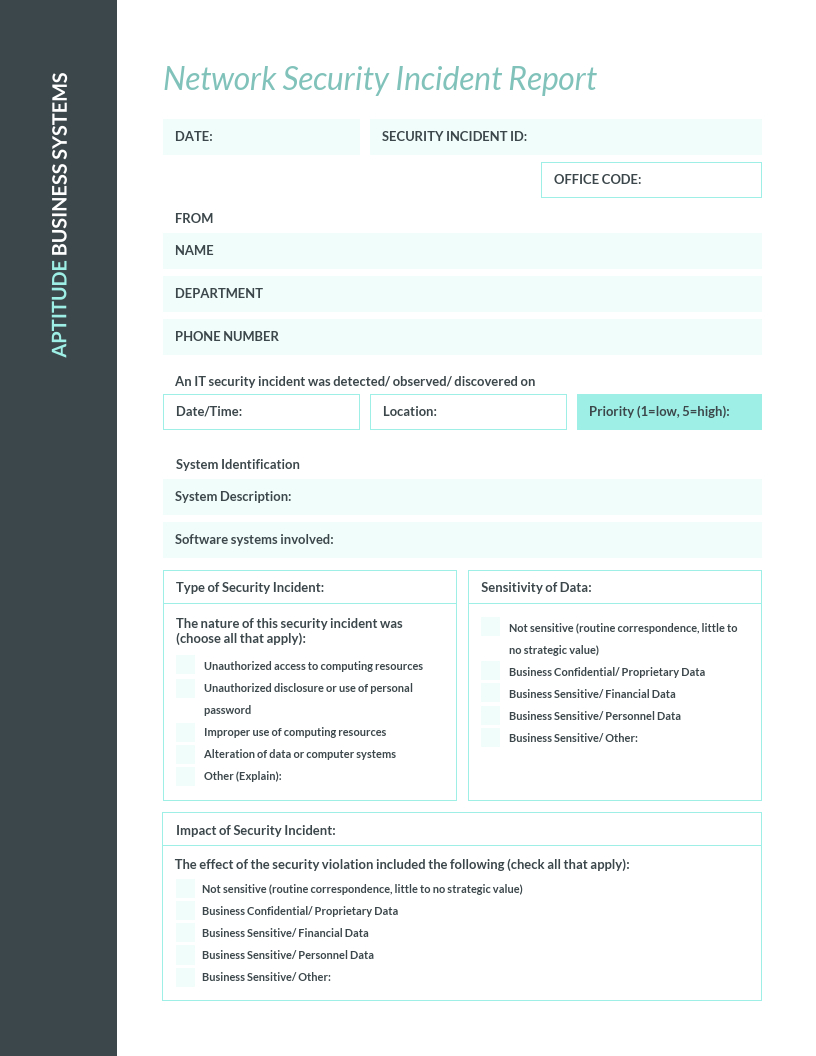
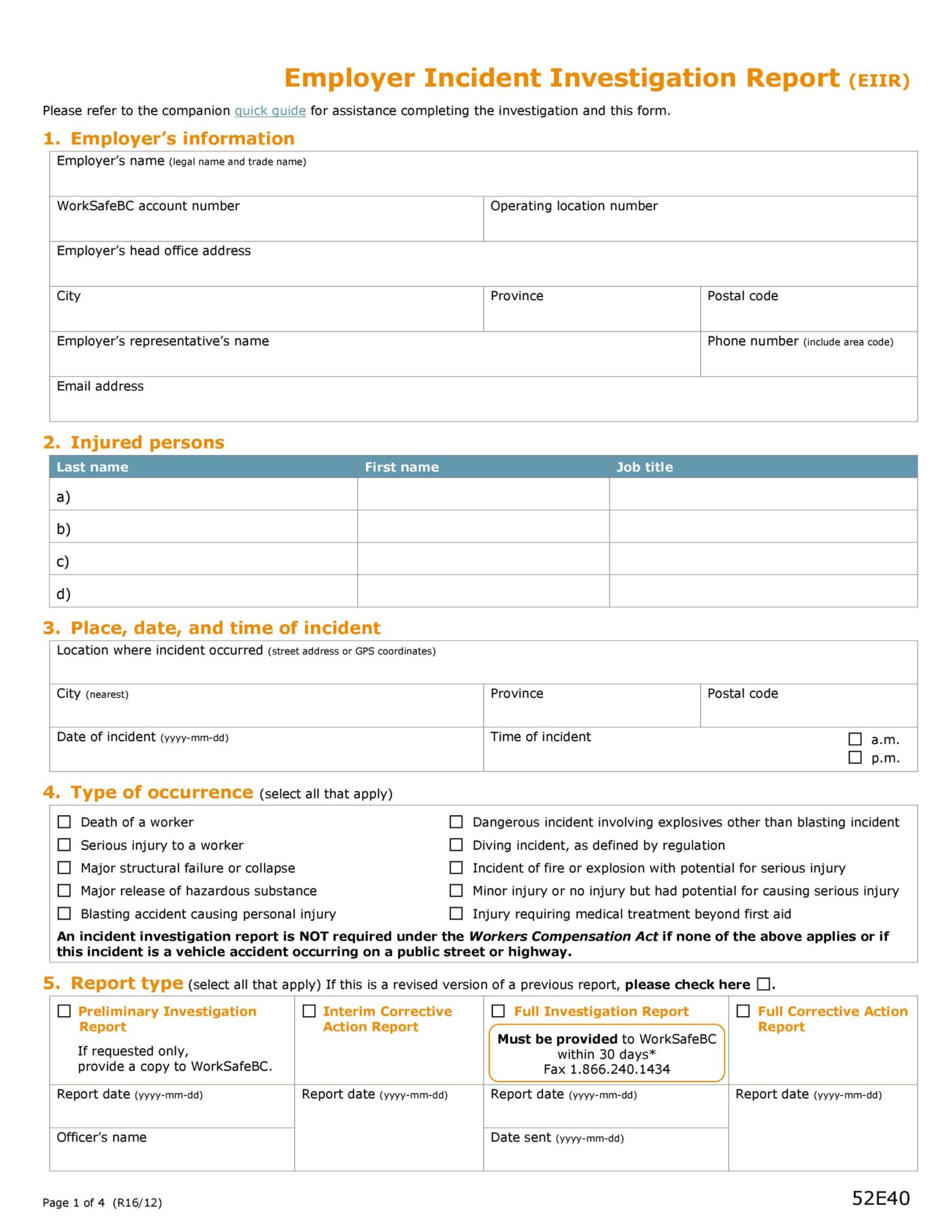
Key Components of an Effective Computer Incident Report Template
A well-designed Computer Incident Report Template acts as a standardized framework, ensuring that all critical information is captured consistently across different incidents and reporting personnel. This consistency is crucial for accurate analysis, efficient response, and effective communication. While specific needs may vary, most robust templates include the following essential sections:
1. Incident Identification and Basic Information
This section captures the fundamental details necessary to quickly identify and categorize the incident.
* Incident ID: A unique identifier for tracking purposes (e.g., INC-2023-001).
* Date and Time of Discovery: When the incident was first identified.
* Date and Time of Occurrence (Estimated): When the incident is believed to have started. This might be different from discovery and is crucial for forensic timelines.
* Reporter Name and Contact Information: Who reported the incident.
* Department/Location: Where the incident occurred (e.g., HR department, specific server rack, remote user).
* Incident Category/Type: A dropdown or checklist (e.g., Malware, Unauthorized Access, System Outage, Phishing).
* Severity/Priority Level: A classification (e.g., Critical, High, Medium, Low) based on impact and urgency.
2. Incident Description
This is the narrative core of the report, providing a detailed account of what happened.
* Initial Observation: A clear, concise description of how the incident was discovered.
* Affected Assets/Systems: List of specific devices, servers, applications, or data involved.
* User Impact: How many users were affected, and what was their experience?
* Technical Details: Any specific error messages, log entries, unusual network traffic, or malicious files identified.
* Timeline of Events: A chronological sequence of observed activities related to the incident.
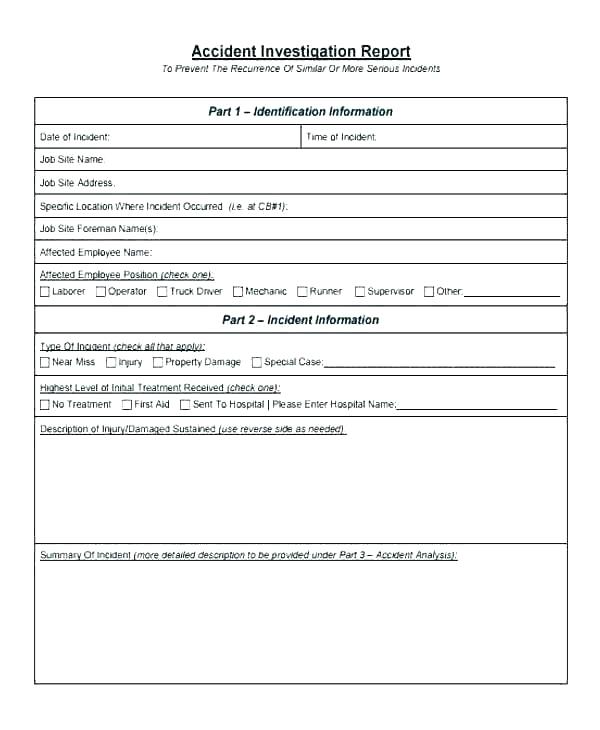
3. Impact Assessment
Understanding the scope and severity of the incident is paramount for appropriate resource allocation and decision-making.
* Operational Impact: Downtime experienced, services disrupted, loss of productivity.
* Data Impact: What type of data was compromised (e.g., PII, financial, intellectual property)? How much data? Was it encrypted?
* Financial Impact (Estimated): Initial estimates of direct costs (e.g., recovery, notification) and indirect costs (e.g., lost revenue, reputational damage).
* Reputational Impact: Potential harm to brand image or customer trust.
* Regulatory/Compliance Impact: Any potential violations of GDPR, HIPAA, PCI DSS, etc.
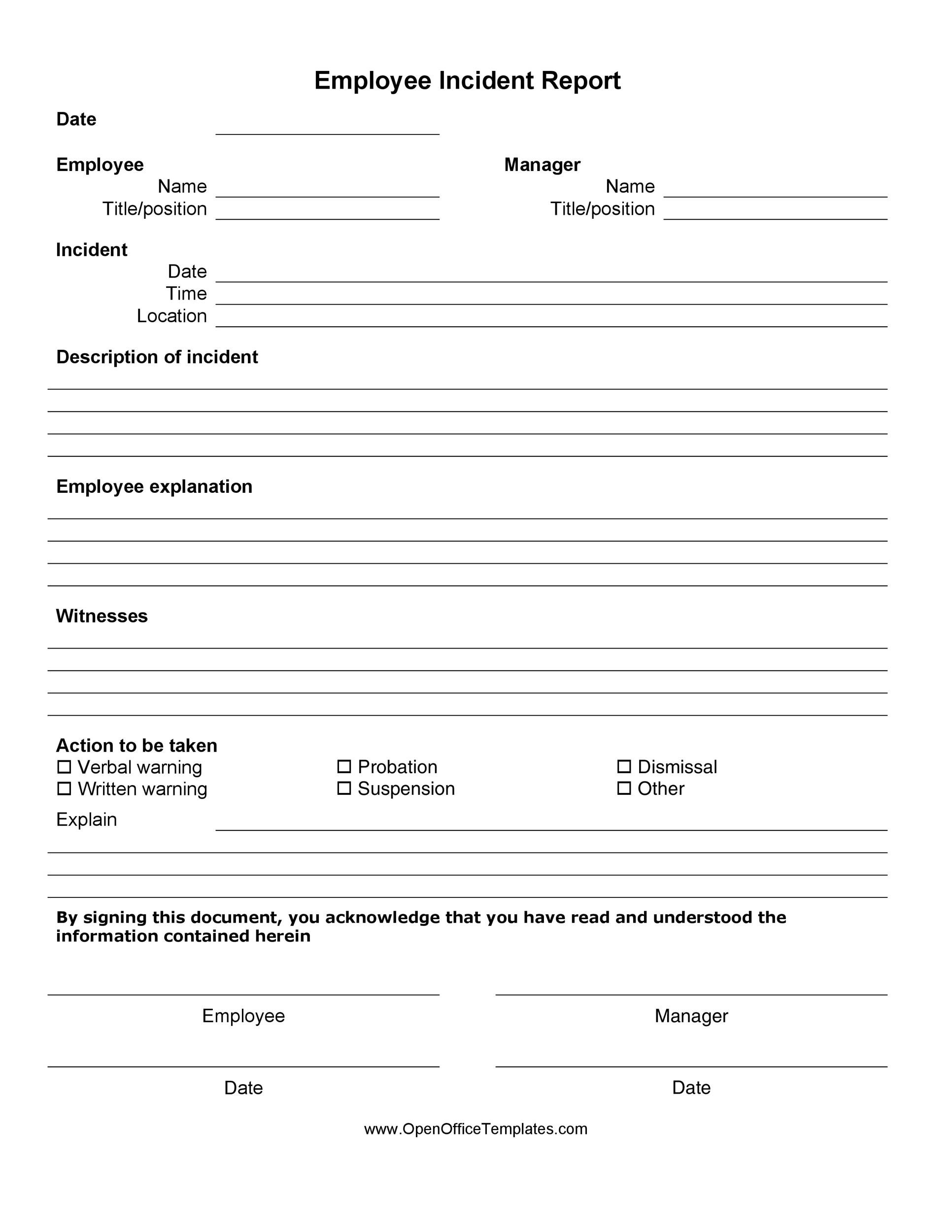
4. Actions Taken and Response
This section documents the steps taken to contain, eradicate, and recover from the incident.
* Initial Response Actions: First steps taken immediately after discovery (e.g., isolated system, changed password, blocked IP).
* Containment Efforts: Measures implemented to limit the spread of the incident (e.g., network segmentation, service shutdown).
* Eradication Steps: Actions to remove the threat (e.g., malware removal, vulnerability patching).
* Recovery Actions: Steps taken to restore affected systems and data to normal operation (e.g., system rebuilds, data restoration from backups).
* Personnel Involved: Names and roles of individuals or teams who responded.
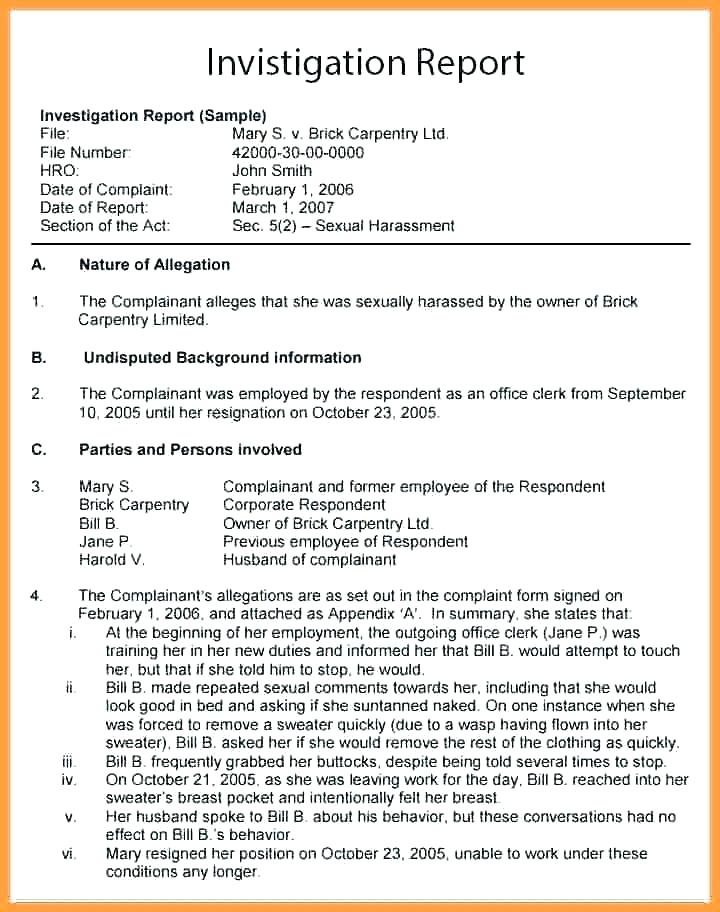
5. Post-Incident Analysis and Lessons Learned
This forward-looking section is crucial for continuous improvement.
* Root Cause Analysis: Identification of the underlying reason for the incident (e.g., unpatched software, weak password, employee training gap).
* Effectiveness of Response: Assessment of how well the incident response plan worked.
* Recommendations for Improvement: Specific actions to prevent similar incidents in the future (e.g., new security controls, policy changes, training needs).
* Outstanding Tasks: Any follow-up actions still pending.
6. Attachments and Supporting Evidence
This section serves as a repository for all supplementary information.
* Screenshots: Visual evidence of error messages, malicious activity, or compromised systems.
* Log Files: Relevant system, application, or network logs.
* Network Packet Captures: For detailed traffic analysis.
* Forensic Images: Copies of hard drives or memory for in-depth investigation.
* Correspondence: Emails, chat logs, or other communications related to the incident.
* Interview Notes: Documentation from interviews with affected users or witnesses.
Benefits of Standardizing with a Computer Incident Report Template
The adoption of a standardized Computer Incident Report Template offers numerous advantages that extend far beyond simply documenting an event. It transforms incident response from an ad-hoc reaction into a structured, proactive process, benefiting an organization’s security posture and operational efficiency.
Firstly, a template ensures consistency and completeness in data collection. Every incident, regardless of who reports it, will capture the same essential information. This uniformity is vital for trend analysis, allowing security teams to identify patterns, recurring vulnerabilities, and the effectiveness of existing controls. Without consistency, comparing incidents or extracting meaningful insights becomes a daunting, if not impossible, task.
Secondly, it significantly improves response efficiency. During a crisis, time is of the essence. A predefined template guides responders through the necessary information gathering steps, preventing omissions and reducing the cognitive load on personnel under pressure. This streamlined process leads to faster containment, eradication, and recovery, ultimately minimizing downtime and financial losses.
Thirdly, templates enhance communication and collaboration. By providing a common language and structure for reporting, it ensures that all stakeholders—from IT and management to legal and public relations—receive information in a digestible and actionable format. This facilitates better decision-making and ensures everyone is on the same page regarding the incident’s status and impact.
Furthermore, a standardized template supports compliance and legal requirements. Many regulatory frameworks (e.g., GDPR, HIPAA, CCPA) mandate specific reporting timelines and information disclosure following a data breach. A comprehensive template helps ensure that all necessary data for these disclosures is readily available, mitigating potential fines and legal repercussions.
Finally, incident report templates are fundamental to continuous improvement. The “Lessons Learned” section, in particular, drives organizational learning. By systematically documenting root causes and recommending preventive actions, organizations can evolve their security policies, improve training programs, and harden their defenses against future threats. It transforms each incident from a setback into a valuable learning opportunity, fostering resilience and proactive security management.
Implementing Your Computer Incident Report Template
Simply having a Computer Incident Report Template is not enough; its effective implementation is crucial. This involves more than just distributing a document; it requires integration into existing workflows, training, and continuous refinement.
Training and Awareness
The most robust template is useless if personnel don’t know it exists or how to use it. Comprehensive training should be provided to all relevant staff, especially those on the front lines of IT support, system administration, and security operations.
* Who to Train: End-users (for initial reporting of suspicious activity), IT support staff (for basic incident handling), and dedicated incident response teams (for detailed documentation).
* What to Train On:
* What constitutes an incident and how to identify one.
* The importance of immediate reporting.
* How to fill out the template, explaining each section’s purpose.
* Escalation procedures and communication protocols.
* Regular Refreshers: Security awareness training should include incident reporting components annually, as threats evolve.
Integration with Incident Management Systems
For larger organizations, integrating the template into an automated incident management system (IMS) or Security Information and Event Management (SIEM) platform can greatly enhance efficiency.
* Automated Fields: Some fields (e.g., date/time of discovery, affected system IDs) can be automatically populated from system logs or alerts.
* Workflow Automation: The system can guide users through the reporting process, assign tasks, trigger notifications, and track progress.
* Centralized Repository: An IMS provides a central database for all incident reports, making them easily searchable and analyzable.
* Reporting and Dashboards: Automated systems can generate reports, dashboards, and metrics based on aggregated incident data, providing valuable insights to management.
Establishing Clear Workflows and Responsibilities
Define clear roles and responsibilities for incident reporting and response.
* Initial Triage: Who receives the initial report and performs preliminary assessment?
* Incident Handler: Who is responsible for leading the response and filling out the detailed report?
* Approvers/Reviewers: Who reviews the completed report for accuracy and completeness before finalization?
* Communication Flow: Who needs to be notified at each stage of an incident, and through which channels?
Best Practices for Incident Documentation
Effective incident documentation goes beyond merely filling in blanks on a form; it requires careful attention to detail, clarity, and timeliness. Adhering to certain best practices ensures that your incident reports are high-quality, actionable, and valuable resources for your organization.
- Be Timely: Document details as close to the event as possible while the information is fresh. Delays can lead to forgotten details and inaccuracies.
- Be Objective and Factual: Stick to observable facts, technical data, and direct quotes. Avoid speculation, assumptions, or blaming language. If you must include an opinion, clearly label it as such and provide supporting reasons.
- Be Specific: Instead of “system was slow,” write “CPU utilization spiked to 98% on Server A at 10:30 AM UTC, affecting database query response times.” Provide exact times, dates, filenames, IP addresses, and user accounts.
- Maintain Chronological Order: When describing the timeline of events, ensure it flows logically from discovery to resolution. This is critical for forensic analysis.
- Use Clear and Concise Language: Avoid jargon where possible, or explain it if necessary. The report should be understandable to various audiences, including technical staff, management, and potentially legal counsel.
- Include All Relevant Evidence: Attach or link to logs, screenshots, network captures, forensic images, and any other data that supports the narrative. Ensure evidence is properly handled to maintain its integrity (chain of custody).
- Regularly Review and Update: The template itself should not be static. As your organization’s IT environment evolves, so too should your incident reporting process and template. Conduct periodic reviews to ensure it remains relevant and effective.
- Secure Storage: Incident reports often contain sensitive information. Ensure they are stored securely, with access restricted to authorized personnel, and retained according to legal and regulatory requirements.
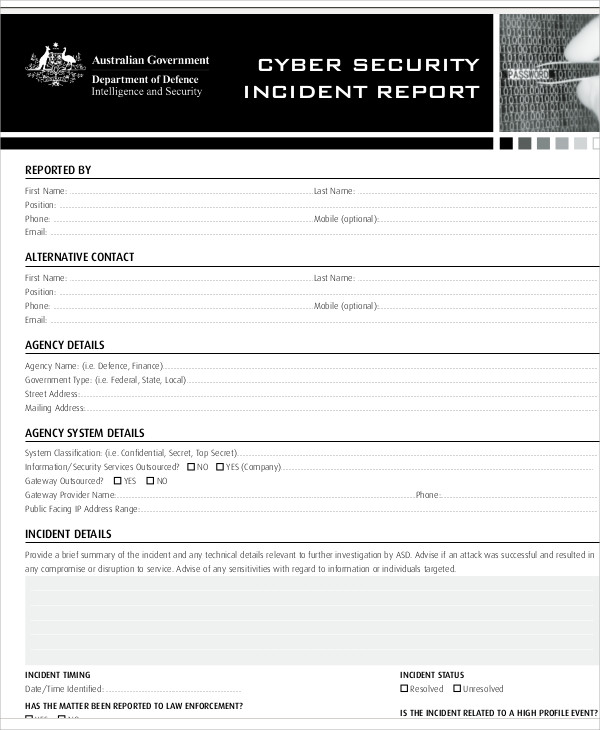
Customizing Your Computer Incident Report Template for Specific Needs
While a generic Computer Incident Report Template provides a solid foundation, effective incident response often requires customization to fit the unique context of an organization. Every business has different assets, regulatory obligations, threat landscapes, and internal processes. Tailoring your template ensures it’s not just a document, but a truly useful tool.
Consider your industry-specific regulations. A healthcare organization, for instance, will need to emphasize protected health information (PHI) and HIPAA compliance in its reporting, potentially requiring specific fields for data types, patient count, and notification timelines. Financial institutions will focus on financial data, transaction integrity, and PCI DSS compliance. Your template should include sections that directly address these unique compliance requirements.
The size and complexity of your IT infrastructure also play a role. A small business might need a simpler template focusing on core assets and basic impact. A large enterprise with multiple departments, cloud environments, and geographically dispersed operations might require more granular detail, such as specific asset tags, cloud service provider details, or regional impact assessments.
Furthermore, think about the types of incidents most prevalent in your environment. If phishing is a constant threat, consider adding specific fields related to email headers, sender details, and user interaction. If hardware failures are common, include fields for asset warranty information, serial numbers, and vendor contact details. Custom sections can also be added for different incident types, such as a dedicated section for “Data Breach Specifics” or “Malware Analysis.”
Finally, involve key stakeholders in the customization process. Your IT team, security operations center (SOC), legal counsel, HR, and even business unit leaders can provide valuable input on what information is most critical for their respective functions. This collaborative approach ensures the template is comprehensive, practical, and aligns with the organization’s overall risk management strategy. Regular reviews and updates based on post-incident analyses will ensure your customized template remains effective and evolves with your organization’s changing needs.
Conclusion
The digital age, with all its advancements, inherently carries risks. Cybersecurity incidents are a challenging but inevitable aspect of operating in this environment. The proactive implementation and diligent use of a comprehensive Computer Incident Report Template is not merely a best practice; it is a fundamental pillar of a resilient cybersecurity strategy. From capturing critical details in the heat of a crisis to facilitating long-term strategic improvements, this template serves as the bedrock for effective incident response.
By standardizing information gathering, enhancing communication, ensuring compliance, and fostering a culture of continuous learning, organizations can transform potential setbacks into opportunities for growth. The systematic documentation of incidents allows for robust root cause analysis, targeted security enhancements, and more informed decision-making across all levels of the business. Investing in a well-defined and regularly updated incident report template, coupled with thorough training and integration into your incident management framework, empowers your organization to navigate the complexities of digital threats with greater confidence, speed, and strategic foresight.
]]>